TRUSTED PARTNER
A leading business intelligence provider for over 30 years across healthcare, social care and education. We work globally with providers, commissioners, payors, manufacturers, investors, regulators and advisors, and are the chosen provider of independent sector healthcare market data to the UK Government’s Office for National Statistics.
FEATURED REPORTS
In-depth analysis of key markets including diagnostics, digital health, hospitals, IVF, dental, medical travel, retirement living, nursing homes, mental health, schools, private equity and more.
FEATURED RESOURCES
Market insight, data and analysis from a trusted business intelligence provider


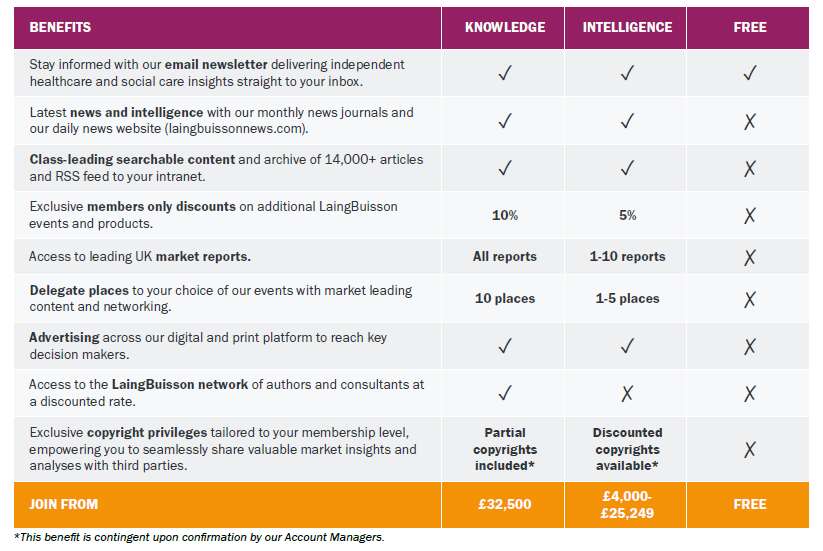
MEMBERSHIP
Grow your business, make better investment decisions and connect with your clients with a LaingBuisson Membership. Join the leading senior executive network in independent healthcare, social care and education. Choose from Knowledge, Intelligence or Insight membership.

JOURNALS
CareMarkets UK, HealthcareMarkets UK, HealthcareMarkets international and the International Medical Travel Journal are the only independent journals providing expert analysis and opinion, with comprehensive coverage of healthcare, social care and education.

NEWS
LaingBuisson News is a Google-approved real-time news feed focused exclusively on M&A deals, financings, people, legal developments, in-depth features and more. This powerful intelligence tool also includes a fully searchable 30-year archive tagged by topic, country and market.

MARKET REPORTS
LaingBuisson’s expert consultants write over 30 regularly updated market reports on all aspects of healthcare, social care and education. Each research document covers market size, segmentation and trends as well as analysis of the political, economic and investment environment

EVENTS
Virtual, on-demand and live conferences and seminars attended by leading senior executives, delivering educational and networking opportunities within independent healthcare, social care, childcare, real estate and medical travel. Many of our webinars are free to attend.

DATA SOLUTIONS
LaingBuisson's data tools enable clients to analyse and export data and deliver sophisticated insights for key markets. Our contact and organisational data subscriptions and services allow clients to communicate with, market to or research a target sector.

CONSULTING
We consult across healthcare, social care, medical devices and life sciences, providing knowledgeable fact-based insights to make the right choices and implement strategies successfully, and have worked in more than 25 countries with over 700 organisations

PATIENT ACQUISITION
Through our well-established network of online consumer portals and printed country and treatment guides, healthcare providers and destinations can promote themselves directly to patients looking to travel for treatment overseas or seeking a second opinion from their clinicians
LATEST HEADLINES
LaingBuisson’s experienced editorial team brings you news of developments and trends across social care, acute care and global healthcare.
MEMBERSHIP
Grow your business, make better investment decisions and connect with your clients with a LaingBuisson Membership. Stay ahead of your competitors with access to proprietary news, analysis and data on your markets that you won’t find elsewhere.
CONSULTING
We consult across healthcare, social care, medical devices and life sciences, providing fact-based insights to make the right choices and implement strategies successfully, and support clients in more than 25 countries within over 700 organisations.
DATA SOLUTIONS
LaingBuisson’s data tools enable clients to analyse and export data and deliver sophisticated insights for key markets. Our contact and organisational data subscriptions and services allow clients to communicate with, market to or research a target sector.
EVENTS
Attracting high-quality, expert speakers, our attendees are sector leaders and CEOs. Topics include Social Care, Housing with Care, Private Acute Healthcare, International Medical Travel, Healthcare Real Estate, Investing in Healthcare and Childcare.
MARKET REPORTS
Our consultants write more than 30 regularly updated market reports on all aspects of healthcare, social care and education, covering market size, segmentation, trends, plus analysis of the political, economic and investment environment.
JOURNALS
Monthly independent digital news journals that concentrate solely on bringing you news of developments and trends in the fields of independent social care, acute care, global healthcare and medical travel. Free trial and sample editions available.
AWARDS
Our annual LaingBuisson Awards and IMTJ Medical Travel Awards are well established in the industry for recognising excellence. Judged independently and objectively, they bring together teams to celebrate outstanding achievement.
PATIENT ACQUISITION
Through our well-established network of online consumer portals and guides, healthcare providers and destinations can promote themselves directly to patients looking to travel for treatment overseas or seeking a second opinion from their clinicians
SOME OF OUR CLIENTS
We have worked in more than 25 countries with over 700 organisations





















MEMBERSHIPS

![]()